A critical warning has been issued for users of Solana-based decentralized finance (DeFi) platforms about a malicious Chrome extension known as “Bull Checker.” This alert was issued by Jupiter, a leading decentralized exchange aggregator on the Solana blockchain, following investigative collaboration with cybersecurity experts and community support.
A Warning for All Solana Users
Jupiter’s research team, in partnership with Offside Labs and key community moderators, uncovered that “Bull Checker” was responsible for unauthorized token transfers from user wallets. Reports began surfacing over the last week about unusual token drains, which prompted a detailed analysis. “Following multiple reports from our users, our investigation identified the ‘Bull Checker’ Chrome extension as a conduit for these thefts,” Jupiter Research writes. The extension, which was supposedly designed to allow users to view holders of memecoins, actually possessed capabilities to alter transaction data.
The extension operates by waiting for a user to interact with a legitimate dApp on the official domain. It then modifies the transaction sent to the wallet for signing. Although the simulation results appear normal, the transactions are manipulated to include instructions that transfer tokens to an attacker’s wallet. “What is particularly insidious about this extension is that it injects malicious code that remains undetected during typical transaction simulations,” added Meow, the pseudonymous founder of Jupiter.
Through technical examination, it was revealed that the attack vectors utilized by “Bull Checker” are sophisticated. “We noticed that the extension could replace the wallet adapter’s signTransaction method with its own implementation, which would then send the unsigned transaction to a remote server. This server attaches a call to a drain program before returning it for user approval,” explained Meow.
This discovery was substantiated by reviewing specific transaction examples where malicious instructions were added to routine transactions. In one of the detailed transaction reviews, the exploited user executed what seemed to be a standard transaction that ended up transferring 0.06 SOL and their token authority to an exploiter’s address identified as 8QYkBcer7kzCtXJGNazCR6jrRJS829aBow12jUob3jhR.
The modus operandi of the malicious extension involved multiple stages. First, the extension monitored the SOL balance of the victim’s account during the transaction simulation, which typically showed a zero balance leading to the abortion of malicious instructions. However, immediately after the simulation, the attacker executed a sequence of bundled transactions that included sending SOL to increase the balance, executing the malicious transaction, and then pulling SOL out, all unbeknownst to the user.
“Bull Checker” was initially promoted through an anonymous Reddit account, known as “Solana_OG,” which appeared to target users interested in trading memecoins. This should have been a red flag given the lack of transparency and the nature of the advertised functionality. Unfortunately, the extension still found its way onto the computers of several unsuspecting users.
The ongoing investigation has revealed that while “Bull Checker” has been identified and publicized, other malicious extensions with similar capabilities might still exist. Users are urged to exercise extreme caution with any extension that requests broad permissions to read and change all data on websites. “Users need to verify the legitimacy and the necessity of any extension, especially those interacting deeply with financial transactions or wallet data,” cautioned Meow.
In response to these types of threats, Blowfish has recently released a feature known as SafeGuard aimed at preventing simulation spoofing attacks, which is now being adopted by multiple Solana wallets. This new security measure enhances the integrity of transaction verifications, providing an additional layer of protection against similar exploits.
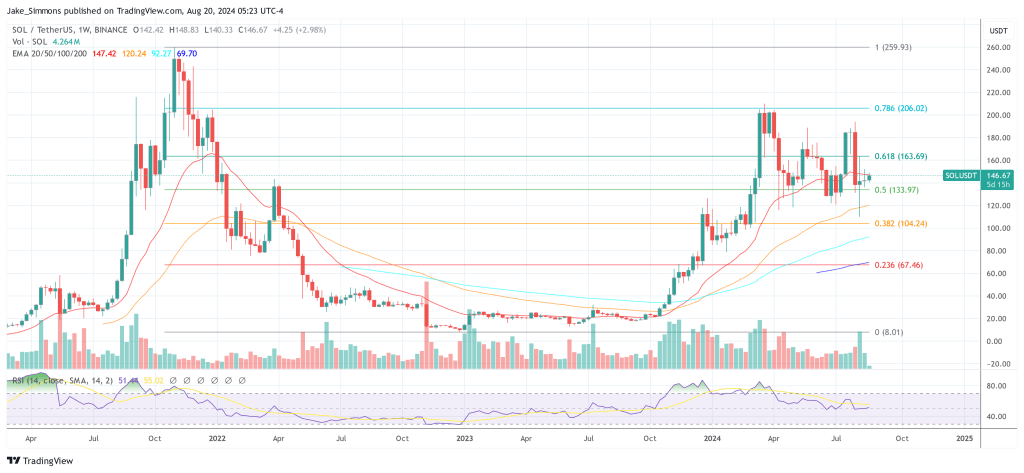
At press time, Solana traded at $146.67.